Reliable, secure maritime email
GTMailPlus secures, optimises and delivers maritime email in the most demanding conditions, working with any satellite provider. Using our enhanced security features and reliable connectivity we make sure that your vessels are always connected.
Email you can rely on
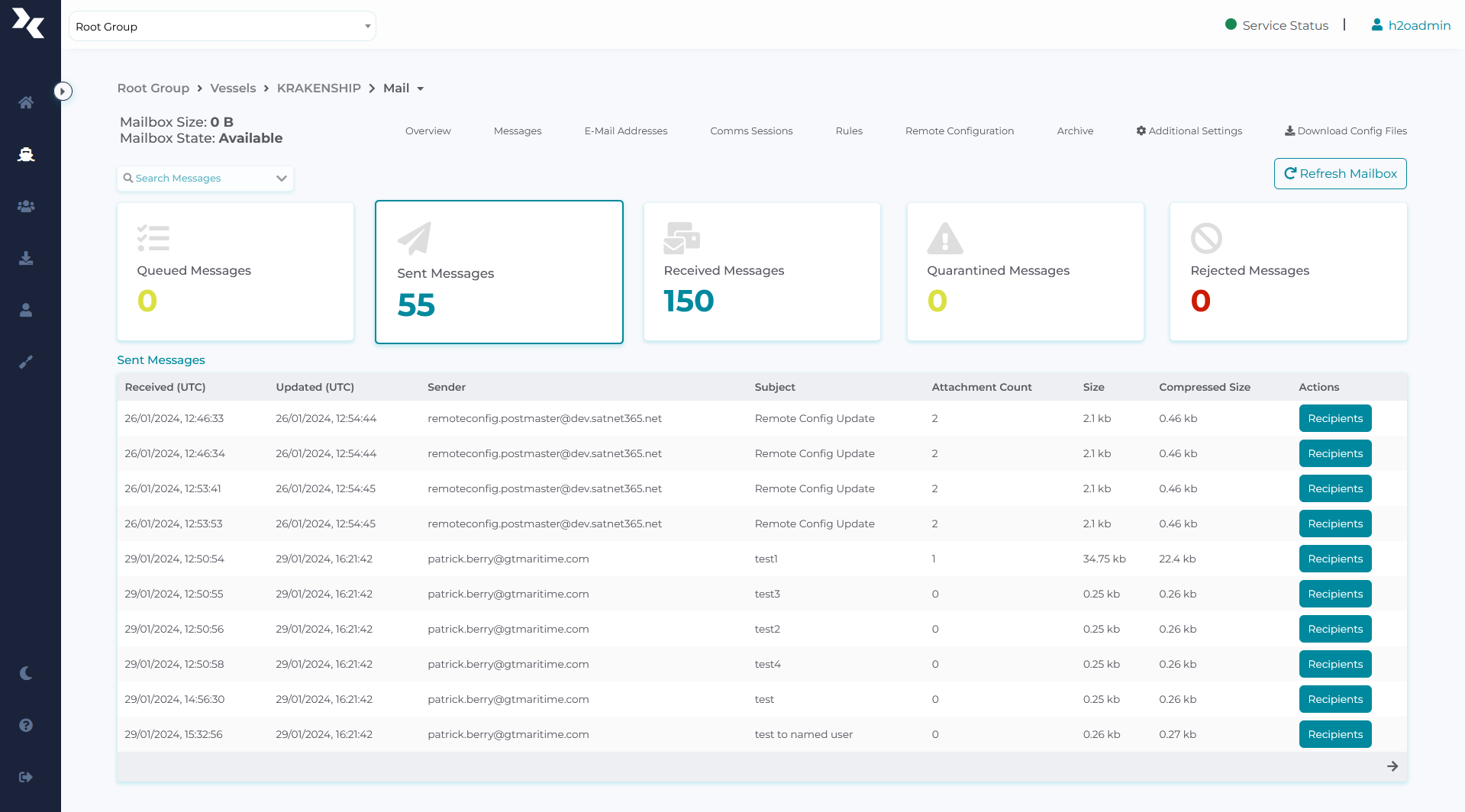
Simple to use and effortless to maintain, our maritime email software can be installed and configured remotely, offering fleetwide management from a single dashboard. GTMailPlus integrates seamlessly with any email client, giving you flexibility and choice. We ensure that your network maintains optimal connectivity with zero loss of data for an efficient service you can rely on. And because bandwidth is only used when it is needed during data transfers, you save on your data costs too.
Efficient email transfer
Resumes transfer from the point of interruption if there is a break or switch in connectivity, saving bandwidth, cost and reducing interruption to crew communications.
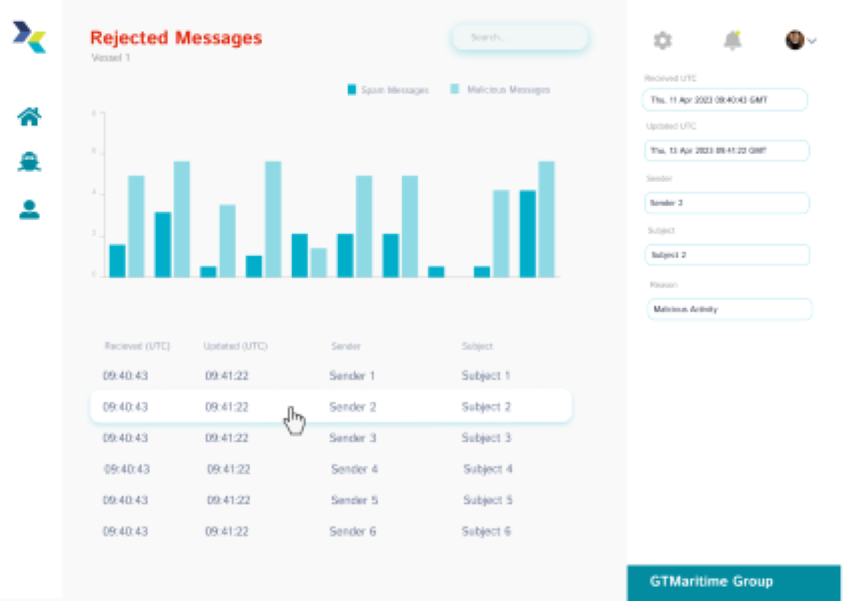
Enhanced security features included as standard
Our comprehensive security suite provides end-to-end encrypted communications, protects against malware, viruses, spam and phishing. Users benefit from a complimentary Dark Web Monitoring for added reassurance.
Flexible email hosting
We can provide you with an email domain or integrate with your shoreside based solution such as Exchange, Office365, Gmail etc. Our email solution is also airtime independent.
Scalable and redundant infrastructure
Working in partnership with AWS, we host servers in multiple locations to ensure high availability and scalability of service.
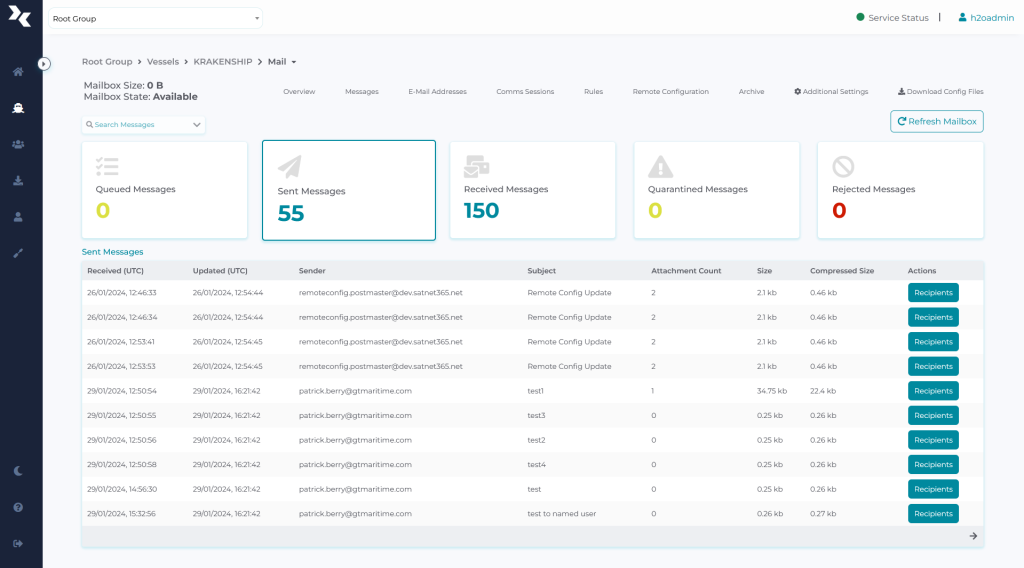
Centralised control, management and audit
Fleetwide remote management and configuration from a single dashboard. Includes pro-active alerts and automated reports.

We provide a back up solution for continuity of service
Authorised users have the ability to send and retrieve emails during any interruption in the shipboard email capability, allowing your business to continue uninterrupted.

24 / 7 support every day of the year
Backed by dedicated support from ITIL trained engineers, available 24/7 to make sure you can access your communications when you need them.
How it works
Our data experts understand the critical importance of communications in the maritime industry and the unique challenges you encounter. The frequency of maritime email based cyber attacks is increasing so it is essential to choose an email platform specifically built to deliver performance, reliability and security at sea.
Industry leading features
Secure your vessel, protect your crew and shield confidential information with our integrated security software that keeps you cyber compliant with enterprise grade security that is included as standard. We ensure vessel compliance, security and business operability 365 days a year.
Anti-Phishing
Comprehensive protection against the latest type of email social engineering attack
Advanced threat protection
Providing protection against zero day threats

Antivirus
Guarding against all known virus signatures through multi-layered detection engines

Spam management
Emails pass through multiple layers of security to ensure your vessels are protected from spam
Archiving
Cloud based maritime archiving, holding emails for up to 7 years
eNOAD
Fully approved software solution for the United States Coast Guard National Vessel Movement Centre

Locator
Allows for the current and historic position of vessels to be viewed
Cloud Access
Ensure you always have access to your emails, from anywhere on any device, even if your systems are offline.
Transfer
Automatically retrieve files and forward to your chosen destination
Dark Web Monitoring
Scans hidden online sources for compromised credentials and sensitive data, alerting customers to potential security breaches before they can be exploited.
Works well with
GTReplicate
File and data transfer optimised for maritime
GTDeploy
Maritime optimised fleetwide software updates
Cyber
Maritime optimised endpoint security
